The InsideIQ Building Automation Alliance, an international alliance of independent building automation contractors, is addressing the issue of cybersecurity and has formed a Cybersecurity Committee to provide education and support to promote best practices in cybersecurity, especially to safeguard BAS networks. The committee will educate InsideIQ member firms about how to better protect themselves and their customers from cyberattacks. The committee will also assist members in the event of a breach with a solid list of first responders and work with cybersecurity experts to evaluate products and practices. InsideIQ recommends a variety of best practices and solutions to protect facilities, businesses and data from the risks of BAS vulnerability. Some solutions work in the short term and need to be implemented immediately to provide protection:
Firewalls // Web-facing control systems need to be configured behind a firewall or virtual private network (VPN) if online access is required. Typically, facilities are using a public IP in the supervisory PC. Firewalls and VPNs are created to be put on the Internet; supervisory PCs and other industry hardware were not.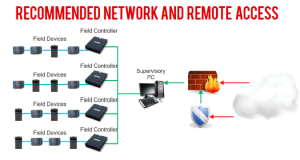
METHOD WILL ENSURE THE BAS IS SECURE. Image: InsideIQ Building Automation Alliance
Passwords // Often BAS networks are established with simple, shared IDs and passwords so that all the facility staff can access the system. At the very least, this password must be changed periodically and especially when an employee leaves. A better system is to use individual IDs and passwords based on policies that dictate creating complex passwords—a rule that must be strictly enforced. Close out user accounts when an employee departs and don’t neglect to remove or change vendor passwords when changing vendors. Furthermore, perform audits periodically to confirm that no one is using unauthorized IDs to access the BAS. User account maintenance needs to be a key part of a facility’s cybersecurity policy.
Education // It is not uncommon for facility staff to surf the Web using a BAS supervisory PC with Internet access. Facility operators must instruct their staff that this activity puts their entire system at risk and must not occur. Train the facility staff to adhere to the user ID/password policy, explaining why this is important and that it is not just a bureaucratic process.
These solutions will go a long way to making a BAS, and subsequently the entire company LAN, safer from cyberattack. Thinking long term, InsideIQ recommends additional measures that building operators can take over time to optimize the safety of the BAS and the network:
Patching // As noted earlier, patching a BAS involves more than a couple of mouse clicks but still may be an effective long-term solution. Beware of the pitfalls: patching sometimes requires a reboot of the supervisory PC and this could negatively impact the downstream field controllers or even require a full system upgrade. Still, this may be the best option to maintain appropriate security for your BAS.
Upgrade // While IT life cycles are usually three to five years, controls systems are expected to have a life cycle of a decade or more. While companies typically budget money for IT life-cycle replacement, funding is rarely available for BAS replacement. As a result, older, at-risk systems remain in place, vulnerable to cyberattack. Like patching, upgrading sometimes creates problems, but it may be the only solution if a BAS is no longer supported by the manufacturer, no patches are available and the facility is perceived to be highly vulnerable.
Protect // It may be necessary to restructure the network and associated hardware to provide the interoperability with remote access and management functionality your facility requires while still maintaining security for the systems and network. This option is typically the easiest and most economical solution to pursue. The following configurations offer the highest security for the BAS:
- BAS connected to corporate LAN and can be accessed internally using a private IP and accessed externally via a VPN to the private IP (See the image on the previous page.)
- BAS connected to corporate LAN and can be accessed internally using a private IP and accessed externally using a secure remote control method (See the image on this page.)
The threats to BAS networks are becoming greater every day and will continue to grow as cyberattackers gain more knowledge about these systems, the critical infrastructure they control and the inherent weaknesses in BAS security. Building owners and operators need to educate facility staff about cyber threats and secure and monitor the BAS network the same as any other IT system. Fortunately, vendors are developing security programs and their products are becoming more secure. Although the threats posed today will remain and new threats will emerge in the future, by implementing appropriate procedures and protocols, control systems can be secured while still providing the benefits of interoperability and remote access that building operators have come to expect.
Online Buzz:
Learn more about the InsideIQ Building Automation Alliance and its Cybersecurity Committee.

