Cybersecurity, network hacking and data theft are topics that seem to be in the headlines on a monthly or weekly basis. Retailers are worried, financial institutions are concerned, and individuals wonder if their identities and credit cards are secure. As a building operator, should you be worried that your building-automation systems (BAS) network could be hacked? Recent research and some emerging anecdotal evidence suggest the answer is yes.
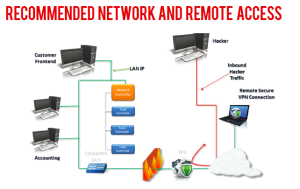
While these scenarios are alarming, they raise the questions why are BAS networks vulnerable and how can hackers gain access to them? The vulnerability of BAS networks lies in the way they have been made interoperable and remotely accessible. Using Internet protocols with Web-based dashboards offers complete building control from workstations in the facility and even remotely from anywhere with an Internet connection, but incorrect assumptions in the underlying architecture to establish interoperability have created unforeseen vulnerabilities.
As originally conceived, BAS networks relying on IP connectivity for interoperability were viewed as too unique to be vulnerable and a philosophy of “security through obscurity” prevailed in the controls industry. According to this line of thought, even if an unintended party accessed the network, the hacker wouldn’t understand what it was. As a result, controls systems for all kinds of buildings and industry are connected to the Internet and have a public IP address that is accessible by anyone or can be accessed from any internal corporate IP address. A significant number of these Internet-facing systems were set up with weak, default or nonexistent login credential requirements for workstations, and sometimes entire networks, and with limited deployment of firewalls, leaving them vulnerable and easily accessible.
But these systems have been on the Internet for years, so why are they only now becoming a target? For the answer, compare the state of BAS network security to that of IT networks for business, commerce government and institutions. These networks have been carefully guarded and protected for years because, historically, hackers have focused on attacking them. As a consequence, network defense is relatively mature and hackers, who don’t discriminate on entry points to an organization, are looking for the weak links that still exist. Without taking appropriate precautions, essentially all elements of a building, such as HVAC, thermostats, automated ID cards, doors, lights, elevators and even the corporate LAN, are open to cyberattack and manipulation through the BAS. With the level of advanced cyberattacks continuing to grow, statistics show that attacks on control systems are only increasing and will continue to do so. If a facility with a BAS connected to the Internet has not been subject to a cyberattack yet, there is a high likelihood that it will be in the near future.
Older BAS technologies are especially vulnerable because these were not designed to handle rigorous security measures, such as encryption. In addition, systems integrators aren’t trained in IT network configuration and security is not part of a typical BAS service agreement. Moreover, system patches for older equipment are rare because manufacturers typically only produce patches for the latest update of their BAS. Unlike patches for desktop computers that happen automatically and quickly, patching a control system usually entails a technician/programmer spending several hours onsite to update the system. Patching a BAS also requires following specific sequences, careful scheduling and complete system recycling, including all the components
and controllers, which can, if mishandled, cause the BAS to crash. For these reasons, patching control systems will likely remain a highly manual and very expensive process for many years to come.

